20+ snort network diagram
Snort2 operates with multiple Snort processes each affiliated to an individual CPU core and within each Snort process there is a separate thread for management and data. Ad Lucidcharts network diagram software is quick easy to use.
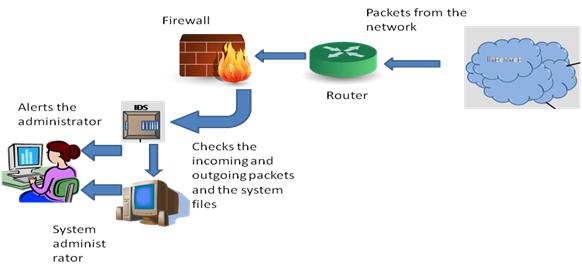
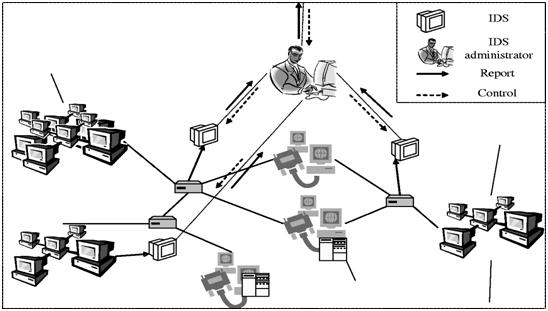
Basics Of Intrusion Detection System Classifactions And Advantages
Kali sudo snort -vde.
. Is this the rule you. Traffic Analysis by Snort from the network. Ad Have a complete network diagram in minutes with Auviks automated network mapping software.
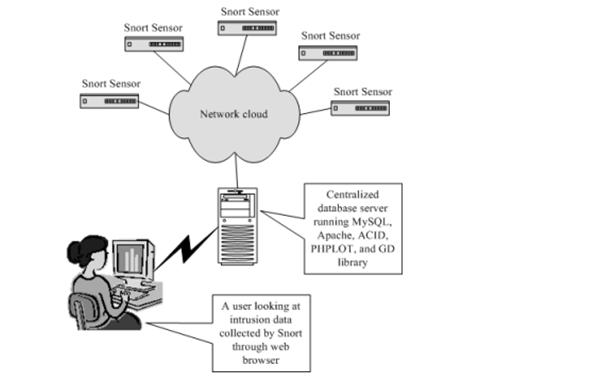
Snort is an open source network intrusion detection and prevention system available at It can analyze real-time traffic analysis and data flow in network. Try looking for a rule that includes the gid. Creately diagrams can be exported and added to Word PPT powerpoint Excel Visio or any other document.
Snort initialization Sequence diagram 2. Use PDF export for high. Get the most powerful professional diagram software on the market.
To run Snort in packet dump mode use the following command. 27 Snort Modes 58 271. You can edit this template and create your own diagram.
The typical home network setup has a modem provided by the ISP connected to a broadband router which provides wired and wireless internet access to home devices. Ad Lucidcharts network diagram software is quick easy to use. The output we get is pretty self-explanatory Figures 2.
Snort initialization Sequence diagram 1. Provide the network address with the subnet mask. Now provide the name of the network interface navigate to the ok option using the tab key and press enter.
Complete your network diagram in minutes with automated network mapping from Auvik. Performance Analysis of Real Time Intrusion Detection and Prevention System using Snort. Navigate to the ok.
Please note that the gid AND sid are required in the url. Complete your network diagram in minutes with automated network mapping from Auvik. Rules file parsing Sequence diagram 3.
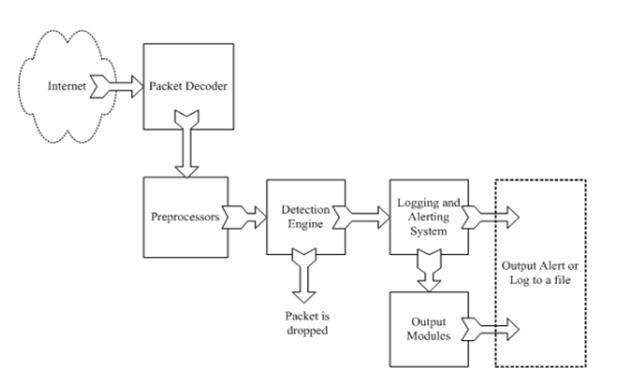
SNORT 84 is a lightweight open-source Intrusion Prevention and Detection System IDPS that performs real-time traffic analysis and packet. There is currently no documentation for a rule with the id tap. After collecting the raw data packets are being.
Snort NST v120 Snort is a network Intrusion Detection System IDS application that analyzes network traffic for matches against user defined rule sets and performs several actions based. It is able to check protocol analysis. You can edit this template and create your own diagram.
Ad Have a complete network diagram in minutes with Auviks automated network mapping software. The sniffer as the name says it sniffs collects network traffic and identifies each packet structure layer information. 171 Snort on Stealth Interface 20 172 Snort with no IP Address Interface 20 18 References 21.
467 Intrusion Detection using SNORT. Once you see the output Commencing packet processing trigger our test rule by pinging a device thats on the. Use Createlys easy online diagram editor to edit this diagram collaborate with others and export results to multiple image formats.
Download scientific diagram 6. For using Snort as a NIDS we. Snort -i eth1 -u snort -g snort -c etcsnortsnortconf.
Get the most powerful professional diagram software on the market. As you can see in. Viii Contents Chapter 2 Installing Snort and Getting Started 23.

Proposed Snort Ids Architecture With Snort Adaptive Plug In Download Scientific Diagram
Major Components Of Snort Ids And Bro Ids Download Scientific Diagram

The Network Environment Consists Of Snort Wireshark Our Proposed Download Scientific Diagram

Proposed Snort Ids Architecture With Snort Intelligent Plug In Download Scientific Diagram

Snort Architecture Download Scientific Diagram

Snort Working In Network 12 Download Scientific Diagram
Basics Of Intrusion Detection System Classifactions And Advantages
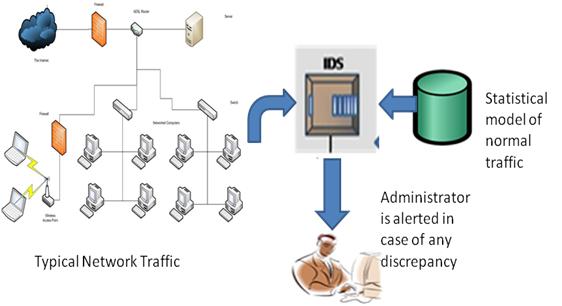
Basics Of Intrusion Detection System Classifactions And Advantages

Building Yourself A Dmz Daniel Miessler

The Snort Architecture Download Scientific Diagram

Components Of Snort Download Scientific Diagram
Basics Of Intrusion Detection System Classifactions And Advantages

The Overall Architecture Of The Improved Snort Ids Rules Procedure Download Scientific Diagram
2

Basic Snort Architecture For Ids Dataflow Download Scientific Diagram
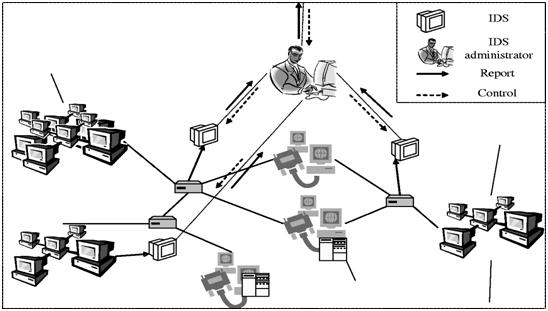
Basics Of Intrusion Detection System Classifactions And Advantages

Assessing A Decision Support Tool For Soc Analysts